Below you will find a comprehensive list of common terms and definitions used in the data collection industry.
0-9
1D Barcode
A one dimensional (1D) barcode is a machine-readable representation of data directly relating to the object it is attached to. A traditional 1D barcode consists of parallel lines that represent numbers or characters. The barcode is read from left to right and can be scanned using a barcode scanner. The most common 1D barcode symbologies are the EAN-13 and EAN-8, UPC-A and UPC-E, Code 128, ITF, and Code 39.
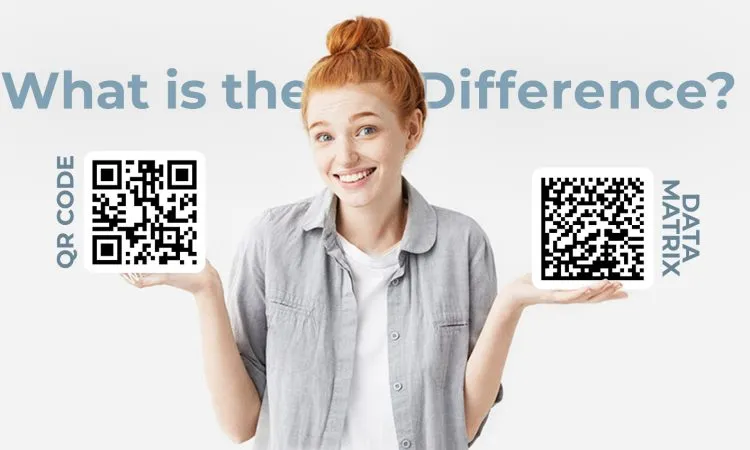
2D Barcode
A two-dimensional (2D) barcode, also known as a quick response code (QR Code), is a machine-readable image attached to items that allows data to be accessed quickly. It stores more information than a one dimensional barcode.
A
Alphanumeric
A series of letters, numbers, punctuation marks, and symbols that can be processed by a computer.
ANSI
Acronym for the American National Standards Institute. Founded in 1918, ANSI is a voluntary organization composed of over 1,300 members (including all the large computer companies) that creates standards for the computerindustry. In addition to programming languages, ANSI sets standards for a wide range of technical areas, from electrical specifications to communications protocols.
Application Temperature
The temperature range at which a label adhesive will properly stick to a product or item.
Aspect Ratio
The proportional relationship between the width and height of an image. It is generally shown as two numbers separated by a colon, as in 16:9.
Asset Tracking
The process of managing a company’s valuable equipment by scanning barcode tags attached to them. This system allows the business to keep tabs on location, stock, condition, and much more information about their items. Learn more »
B
Barcode Symbology
The technical details of a certain type of barcode, such as the width of the bars, character set, method of encoding, and checksum specifications. Symbologies contain systems of encoding data that a scanner or decoding system may read and decode.
Barcode Verifier
A barcode verifier works the way a reader does, but instead of simply decoding a barcode, a verifier performs a series of tests to ensure the scanability and quality of the barcode in comparison to industry standards and specifications. Barcode verifiers are primarily used by businesses that print and use their own barcodes.
Batch Processing
In data collection, this system is where a mobile computer is used to collect and process a group of data by scanning barcodes on your inventory or assets. Once all data has been entered, the mobile computer can be connected to a PC and the information can be dumped into it all at once. This method does not require a constant connection between the mobile computer and your PC as in a real-time system.
Bluetooth
A short range radio technology aimed at simplifying communications among Internet devices and between devices and the Internet. It also aims to simplify data synchronization between Internet devices and other computers.
C
.csv File
Also known as Comma Separated Values, this file format is a way to store large amounts of data. Commas separate the data values and include a header describing what data is populating the file. The most popular program to write and maintain .csv files is Microsoft Excel, but Notepad and other minimal text-editors can also be used to read and write .cvs files.
CAC (Common Access Card)
A “smart” card that is the size of a credit card. Most commonly, CAC cards enable physical access to buildings and controlled spaces. It can also provide access to computer networks and systems. It uses ditigal signatures and data encryption technology, such as authentication, integrity and non-repudiation. The CAC contains a PDF417 barcode on the front of the card and a Code 39 barcode on the back.
CDMA
Code Division Multiple Access is a digital wireless technology for communication between devices and is also used by major cell phone carriers like Sprint and Verizon Wireless. CDMA employs “spread-spectrum” technology, which means that it spreads the information contained in a particular signal of interest over a much greater bandwidth than the original signal. Special coding in CDMA allows it to have no hard limit on the number of users who may share one base station.
Check Character
An extra character added to the end of a block of transmitted data to check the accuracy of the transmission.
Code 128
A symbology that encodes alphanumeric data in applications where a large amount of data must be encoded into a small amount of space. The data is encoded by including a checksum digit and is verified character by character. The Code’s character set includes the letters A-Z, digits 0-9, and all ASCII symbols and control codes.
Code 2 of 5
A continuous two-width barcode symbology that encodes pairs of digits. It is used commercially on ITF-14 barcodes, 135 film, and product containers.
Code 39
Also known as Alpha39, Code 3 of 9, Code 3/9, Type 39, USS Code 39, or USD-3, this barcode symbology varies in length. It defines 43 characters, which consist of uppercase letters, numeric digits, and special characters. The ‘*’ character is also used for start and stop delimiters. Code 39 was the first alpha-numeric symbology to be developed, and it is used by the United States Department of Defense, the Health Industry Bar Code Council, and in non-retail environments.
CodeGate
This program works hand-in-hand with Metrologic’s patented automatic-triggering scheme; simply present a barcode to a Metrologic scanner. The high-visibility 650-nanometer laser is automatically activated allowing the user to easily select the barcode to be scanned. Press the CodeGate button and the data is transmitted to the host system.
Contact Scanner
A contact 3D scanner can scan an item through physical touch while the item is on a precision flat surface plate.
Cordless
Any electronic device that is powered by a battery and can function without a power cord or cable. Cordless does not mean wireless, even though some commonly used items, such as cordless telephones, are wireless.
D
A two-dimensional matrix barcode in the shape of a square or rectangle consisting of black and white cells that represent bits. The information to be encoded can be text or numeric data that ranges from a few bytes to 1556 bytes. Each DataMatrix code is unique and can store up to 2,335 alphanumeric characters.
Depth of Field
The distance from the front of a scanner to the barcode it is trying to read.
Direct Thermal
A digital printing process which uses a thermal print head that applies heat to coated thermal paper. Direct thermal printing does not require a ribbon. The image is produced directly on the printed material as the coating turns black in areas where it is heated. There are also direct thermal printers that can print two colors, often black and red, by applying heat at two different temperatures.
Direct Thermal Paper
Paper coated with a colorless formula that develops an image when heat is applied to it. This paper is used by Direct Thermal printers.
Dot Matrix
A 2-dimensional pattern of dots that is used to represent clear and accurate characters, symbols, or images. The human eye blends the dots together to create a coherent image. Therefore, the more dots used, the more coherent and clear the image appears to be. They are used for electronic displays, including cell phones, televisions, computer screens, LED screens and printed output. For example, a newspaper is made up of dot matrixes, but it is difficult to notice unless you look very closely at the paper.
DPI
Dots per inch (DPI) is a measurement of printer resolution that defines how many individual dots can be placed in a line within the span of 1 inch when the image is printed. DPI is commonly confused with PPI. DPI refers to the resolution of the printer, where as PPI refers to the resolution of the image itself. Photo-quality ink jet printers have a DPI resolution in the range of 1200 to 4800 dpi.
DRAM
Dynamic random access memory, or DRAM, is the most common type of computer memory. It is particularly useful for computers as it can hold a lot of data in a small physical space. However, it does not usually retain data when its power supply is switched off, meaning that it isn’t suitable for permanent storage.
Driver
Software and/or firmware that controls hardware and often connects an operating system with specific hardware devices, allowing them to properly work in unison. Software refers to a program sunning on hardware while firmware is a semi-permanent software that is placed into the hardware. Firmware does not disappear when the hardware is turned off and, in order to change the firmware, it must be done by a special installation process.
Duty Cycle
The percent or ratio of time that a component, device, or system is operated. If a disk driver operates for 1 second, then is shut off for 99 seconds, and keeps repeating that process, the drive runs for one out of 100 seconds. Its duty cycle is 1/100, or 1 percent. The higher percentage value of the duty cycle, the shorter the useful life of the device will be.
E
EAN
There are different types of EAN barcodes. The most common is the EAN-13, which is a 13 digit barcoding standard that includes 12 numbers and 1 check. These barcodes are used worldwide in retail stores, and the numbers encoded in them are product identification numbers. The less common EAN-8 barcode is used for marking smaller retail goods. Also, an EAN-2 and EAN-5 are supplemental barcodes that may be added to an EAN-13 barcode for a total of 14 or 17 data digits. The supplemental barcodes are often needed for periodicals, books or weighed products.
ECW
Enhanced Compression Wavelet is an image compression format, originally used for aerial and satellite imagery. The lossy compression format efficiently compresses very large images with fine alternating contrast.
ERP
Enterprise resource planning (ERP) systems is an automated business management software that uses integrated applications to manage the information of an entire organization. The purpose of ERP is to facilitate information between all business functions inside an organization and manage connections to outside stakeholders. ERP systems can run on a variety of computer hardware and network configurations.
ESD
Electrostatic discharge (ESD) is the sudden surge of electricity between two objects caused by a buildup of static electricity. ESD has the potential to cause a range of harmful effects and even permanent damage in any industry, including failure of solid state electronics components such as integrated circuits or even barcode readers. Many steps should be taken to protect your data capture hardware from the risk of ESD, especially in a manufacturing environment.
F
Flash Memory
An electronic, non-volatile computer storage device that does not require power to retain data. It can be electrically erased and reprogrammed.
Floodcoat
This refers to the colored coating on certain barcode labels. With a variety of color options, company’s use these labels to simplify product identification and make picking and organization much easier.
Font
The combination of properties for a set of characters including typeface, size, pitch, and spacing. Typeface is the most important quality of a font because it defines the shape of each character. The size refers to the character’s height (which is measured in points) and the pitch indicates the number of characters displayed per inch. Spacing is the distance between all characters in a word.
G
Global Standards One (GS1) is an international non-profit association dedicated to the development and implementation of global specifications to management of supply and demand chains across multiple sectors.
GS1 DataBar
These symbols can carry more information and identify smaller items than EAN and UPC barcodes. GS1 DataBar utilizes GTIN identification for fresh variable measure and hard-to-mark products like loose produce, jewelry and cosmetics. Additionally, GS1 DataBar codes can carry GS1 Application Identifiers such as serial numbers, lot numbers, and expiration dates, creating solutions to support product authentication and traceability for fresh food products and couponing.
GSM
Global System for Mobile Communications is a standard set by the European Telecommunications Standards Institute (ETSI) to describe protocols for second generation (2G) digital cellular networks used by mobile phones and devices. This was expanded over time to include data communications via GPRS (General Packet Radio Services) and EDGE (Enhanced Data rates for GSM Evolution or EGPRS).
GTIN
Global Trade Item Number (GTIN) is an identifier for trade items developed by GS1 that is used to locate product information in a database. GTINs may be 8, 12, 13 or 14 digits long and are used by many different industries, including retailers, manufacturers, collectors, and researchers. A GTIN is unique and universal, which makes it useful in establishing the correlation between products in different databases.
H
HSDPA
High-Speed Downlink Packet Access (HSDPA), also known as 3.5G, 3G+ or turbo 3G, is a 3G mobile telephony communications protocol in 3, which allows networks based on Universal Mobile Telecommunications System (UMTS) to have higher data transfer speeds and capacity.
Human Readable
This term refers to a format of information that can be read and comprehended by humans. It is often encoded as ASCII or Unicode text, and almost all data can be converted into a human readable format by a suitably equipped and programmed computer or machine. A common example is when a scanner converts a barcode into a human readable format onto a PC.
I
Interface
The point of interaction between hardware and/or software components. These components function independently while using the interfaces to communicate with each other through an input/output system and an associated protocol. The most common interface is USB.
Interleaved 2 Of 5 Code (I 2 of 5)
Interleaved 2 of 5 is a continuous two-width barcode symbology that encodes any even number of numeric characters in widths and spaces of a barcode. The symbology is called “interleaved” because the first digit is encoded in the five bars (or black lines), while the second digit is encoded in the five spaces (or white lines). This way, the first 5 bars and spaces actually encode two characters. Interleaved 2 of 5 is typically used in the distribution and warehouse industry.
Inventory Management
This is the process of efficiently tracking and controlling the constant flow of items in and out of an existing inventory; preventing it from becoming too high, or dwindling to levels that could put the company’s operation in jeopardy. Competent inventory management also seeks to control the costs associated with the inventory, both from the perspective of the total value of the goods included and the tax burden generated by the cumulative value of the inventory.
IP Rating
The Ingress Protection (IP) Rating classifies and measures the degree of protection a device offers from the intrusion of solid objects such as body parts, dust, accidental contact, and water into its electrical enclosures. The digits following “IP” represent the conformity with certain conditions. The first number is the level of solid particle protection the device offers, while the second number refers to its amount of liquid ingress protection. The higher the numbers, the more durable and rugged the device is. If a condition does not have a protection rating, it is marked with the letter X. An IP22 or IP2X are typical minimum requirements for the design of indoor electrical accessories.
IrDA
The Infrared Data Association (IrDA) is an industry driven group of device manufacturers that developed a standard for transmitting data via infrared light waves. IrDA provides specifications for a complete set of protocols for wireless infrared communications. Many mobile phones, laptops, cameras, scanners, mobile computers, and printers come with IrDA ports that transfer data using the “point and shoot” principle, which enable you to transfer data from one device to another without any cables.
The International Standard Book Number (ISBN) is a unique numeric commercial book identifier. It is a number, not a barcode, printed on books. The ISBN identifies the title or another similar book-like feature to which it is assigned.
ISO
The International Standards Organization (ISO) is a well known and respected developer of international barcoding and data capture standards. It was the leading contributor in the development of global standards supporting the GS1 barcode System.
J
jPOS
A free and open source library/framework that can be used to implement financial interchanges.
K
L
M
Mobile Computer
Also known as a portable data collector or portable data terminal (PDT), a mobile computer is a barcode scanner with a display and an operating system. People most commonly refer to a mobile computer as a cordless barcode scanner. A mobile computer allows a user to capture data on the move without having to be connected to a network to access information since it can store it internally.
MS SQL
Microsoft SQL Server (MS SQL) is a relational, cloud-ready database management system developed by Microsoft that stores and retrieves data as requested by other software applications. There are many different editions of Microsoft SQL Server for different audiences and workloads. The programs range from small applications that store and retrieve data on the same computer, to much more advanced systems that support millions of users and computers accessing large amounts of data from the Internet simultaneously.
N
Non-Incendive
This is an attribute seen in some rugged, hazardous environment mobile computers. Environments in which ignitable concentrations of flammable gases, combustible dusts, or ignitable fibers are likely to exist require the use of intrinsically safe devices and non-incendive devices contain circuits with the ability to spark under normal operating conditions, but they do not release enough energy to cause an ignition.
O
Omni-directional
This refers to the scan pattern of certain barcode scanners. These scanners work like any laser barcode scanner with the addition of several mirrors and other reflective devices to transform the single laser line into many, all at different angles. This allows fast reading of barcodes at any angle, making an omni-directional barcode scanner perfect for point of sale installations, such as at a grocery store.
Operating Temperature
This is the temperature range at which a mechanical or electrical device functions properly. This range varies based on the device’s function and the application it is being used for. Operating a device outside of the given range will likely cause it to fail.
P
PDF417
The new standard for identification that uses a stacked linear barcode symbol format and has become the preferred means of encoding ID information. It is used for a variety of purposes, including identification cards and inventory management. PDF stands for Portable Data File. The 417 signifies that each pattern in the code consists of 4 bars and spaces and that each pattern is 17 units long. A PDF417 can store and transfer large amounts of data securely and inexpensively. It carries up to 1.1 kilobytes of machine-readable data and it can also contain text, numbers, graphics, photographs, fingerprints, and signatures.
Piggyback Label
A pressure-sensitive label that allows for dual usage and is made from facestock, adhesive, and liner.
Platen Roller
A platen roller is a vital printer component that helps create the optimum amount of pressure to drive labels through the printer, ensuring clean and crisp printouts. Replacing a worn or damaged platen roller immediately will help ensure continued top-notch printer performance and avoid costly downtime.
Point of Sale (POS)
Commonly referred to as the “checkout,” the POS is where a retail transaction is completed when a customer makes a payment to a merchant in exchange for goods or services. POS systems consist of these 7 core components – a PC, software, display (a customer display in addition to a typical monitor), barcode scanner, credit card reader/payment terminal, cash drawer, and receipt printer.
Portable Data Terminal (PDT)
A portable Data Terminal, or mobile computer, is an electronic device with a built-in monitor that serves as a barcode reader to enter or retrieve data through wireless transmission. It can be used in large stores, warehouses, hospitals, or in the field to access a database from a remote location. PDT’s can interact with a database or software application by running wireless device management software.
POSTNET
Postal Numeric Encoding Technique (POSTNET) is a barcode symbology used by the United States Postal Service to assist in directing mail. The ZIP Code or ZIP+4 code is encoded in half and full-height bars. Often the delivery point is added, usually being the last two digits of the address or PO box number.
Powered USB
Powered USB (also known as Retail USB, USB Plus Power, and USB + Power) is a single cable connection that allows higher-power devices to obtain power from a PC. Powered USB maintains the standard USB interface for data communications and adds a second connector for extra power. It is most commonly used in point-of-sale equipment, such as receipt printers and barcode readers.
Print Contrast
This is a method of evaluating and optimizing the density of the ink deposited on the substrate during printing and is calculated by measuring the ink density of a solid area and the ink density in a 75% tint.
Q
QR Code
A Quick Response (QR) code is a popular type of 2D barcode embedded with information related to an item it is printed on or attached too, commonly seen on billboards and ads. QR codes have faster readability and greater storage capacity than standard barcodes. The code typically consists of black modules arranged in a square grid on a white background (or any other combination of contrasting colors). The information encoded may be made up of four standardized types of data including numeric, alphanumeric, byte/binary, and Kanji. A QR code is read by an imaging device and formatted algorithmically by underlying software. Data is extracted from patterns present in both horizontal and vertical components of the image. A variety of industries use QR codes to run different applications such as product tracking, item identification, time tracking, document management and general marketing purposes.
QWERTY
This is the most common keyboard and keypad layout. Its name is derived from the first six letters on the top letter row of the keyboard.
R
Raster
A raster, or bitmap, is a computer graphics image that represents a dot matrix data structure and contains a grid of pixels. It is viewable on a monitor, paper, or any other display medium. Raster images are stored in different formats in image files.
Real-time Processing
In data collection, this method is where a mobile computer is used to collect data by scanning barcodes on your inventory or assets and, in real-time, communicates that information back to your PC. This process requires a constant connection between the mobile computer and your PC such as a wireless network or Bluetooth, unlike in a batch system.
Resin Ribbon
This ribbon type is designed to print onto plastic labels by dissolving into the plastic surface of the label, creating a high degree of adhesion and durability. Resin printed plastic labels are scratch-resistant and can withstand sunlight, water, chemicals, and oils.
RFID
Radio-frequency identification (RFID) is the wireless use of radio-frequency electromagnetic fields to transfer data automatically in order to identify and track tags attached to objects. Some tags do not require batteries and are powered and read through magnetic fields, while other tags use a local power source and emit radio waves. Unlike a barcode, an RFID tag can be read from up to several meters away, multiple tags can be read simultaneously, and they may be embedded within a tracked object. RFID tags can be attached to many items such as clothing, automobile parts, and pharmaceutical items. Many pets and livestock may have RFID tags injected, which allows them to be easily identified.
ROM
ROM is an acronym for read-only memory. Data on a ROM device, such as a disk or chip, cannot be removed or modified. Most computers contain some ROM that stores critical programs. ROMs are also used in other devices such as mobile computers and some printers.
RS-232C
Short for recommended standard-232C, this is a standard interface approved by the Electronic Industries Alliance (EIA) for connecting serial devices, such as older label printers, to other devices such as a computer. RS-232 describes the physical interface and protocol for low-speed serial data communication.
S
Scan Gun
Another term for a handheld barcode scanner or mobile computer with a gun grip, a scan gun is used in conjunction with a PC to read barcodes.
SKU
A Stock Keeping Unit (SKU) identifies each distinct product or service offered by a business. A SKU does not need to be assigned to tangible products in inventory. Instead, they are applied to intangible, billable products, such as units of repair, time, or warranties. For this reason, a SKU can be thought of as a code.
T
Tamper Proof Label
Tamper proof, or tamper evident, labels mark someone’s property and provide extra security for particular items. A tamper proof label is a pressure sensitive label made of a weak material that will break or disintegrate when you try to remove them. Certain tamper proof labels are comprised of materials that leave a mark on the surface of the product and display a message that shows the label and product have been tampered with, such as “void.” Tamper proof labels can be barcoded or sequentially numbered.
Telepen
This is a barcode symbology that does not define independent encodings for each character. It is comprised of all 128 ASCII characters without using shift characters for code switching and uses only two different widths for bars and spaces.
Terminal Emulation
A terminal emulator, terminal application, term, or tty for short, is a program that connects to a mainframe computer or bulletin board service with a personal computer. A user is able to access various machines text terminals and applications through one terminal window. Typically, terminals support escape sequences for controlling color, and cursor position.
Thermal Transfer
The digital printing process in which material is applied to paper (or some other material) by melting a coating of ribbon so that it stays glued to the material on which the printed image is applied. It produces longer lasting labels than direct thermal printing and differs from it since no ribbon is present in the direct thermal process.
Thermal Transfer Paper
This type of label paper is made of heat-sensitive material used in thermal printers consisting of four layers: a yellow sheet, a protective sheet, a white sheet, and the carbon layer. The paper changes colors when it is coated with a chemical and heated.
U
UID Tag/Label
Unique Identification (UID) marking is a part of the compliance process mandated by the United States Department of Defense. It is a permanent marking method used to give equipment a unique ID to improve asset management. It is a set of data for tangible assets that is unique and unambiguous worldwide and also ensures data integrity and quality while supporting many business applications and uses.
UPC
Universal Product Codes (UPCs) were originally adopted by grocery stores to expedite the checkout process and track inventory, but they are now used among many types of retail products at the point of sale, most of which adhere to GS1 specifications. UPC codes contain two parts: a machine-readable barcode and a human-readable 12-digit UPC number. The manufacturer identification number is the first six digits of the UPC number, and the next five digits are the item number.
USB
Universal Serial Bus (USB) is a standardized means of physical connection between devices for purposes of communication or connection to a power supply. A USB cable can connect a computer to scanners, keyboards, digital cameras, printers, smartphones, and much more.
V
Verifier
See “Barcode Verifier.”
W
WAN
A Wide Area Network (WAN) is a telecom network that uses private or public network transports and spans across metropolitan, regional, or even national boundaries. Businesses and government entities use WANs to relay data among employees, clients, buyers, and suppliers regardless of location. The Internet is the most popular WAN.
Wax Ribbon
This is used for printing either matte or semi-gloss paper labels. These labels can last for years, although exposure to water, chemicals, oil, or abrasions can destroy the wax image.
Wax/Resin Ribbon
A wax/resin ribbon produces a finer image on smooth or coated label paper and it is more durable than wax. It can withstand minor exposure to water or moisture.
Wedge
See “Keyboard Wedge.”
WEH
Windows Embedded Handheld (WEH) is an operating system optimized for enterprise handheld devices that enable a mobile line of business applications with secure and efficient data input. WEH is used in many industries for different purposes, including field mobility, transportation and logistics, retail, healthcare, and manufacturing.
Windows CE
Microsoft Windows CE, known as Windows Embedded Compact, is a distinct operating system for embedded systems. Microsoft licenses Windows CE to OEMs and device makers who can modify and create their own user interfaces and applications within the program. Windows CE is compatible with Intel x86, MIPS, and ARM processors.
WIP
In supply chain management, Work in Process (WIP), or in-process inventory, refers to a company’s partially finished goods. Barcode and RFID identification are used to identify and locate work items in a process flow.
Wireless
Wireless communication allows for the transfer of information between multiple points without the need for a physical connection between those points. In data collection, wireless options exist in scanners, mobile computers, tablets, etc.
X
X dimension
The X dimension is the narrowest part of a barcode, used to determine the amount of information a barcode can capture within a certain amount of space. Generally, barcodes with a greater X dimension are easier to scan.
XML
Also referred to as Extensive Markup Language, XML defines a set of rules for encoding documents in a format that is both human-readable and machine-readable. XML design focuses on documents but is also widely utilized for arbitrary data structures such as web services. XML formats have also become the standard for many office productivity tools such as Microsoft Office and Apple iWork.
Y
Z
ZPL/ZPL II
Zebra Programming Language (ZPL) is a printer control language, primarily used for labeling applications. ZPL is the original language, which was later advanced by ZPL II and eventually by ZBI, which avoids refactoring of code when changing the printer.